Implementing Secure by Design in UK HMG: A Comprehensive Approach with NIST and NCSC Guidance
Implementing Secure by Design in UK HMG: A Comprehensive Approach with NIST and NCSC Guidance

In an increasingly digitised world, cyber threats have become a pressing concern for governments and organisations worldwide. The UK government has taken a proactive stance on cybersecurity by adopting the principles of Secure by Design (SbD). This approach prioritises embedding security measures at the earliest stages of system development, ensuring resilience against evolving cyber threats. Leveraging guidance from the National Institute of Standards and Technology (NIST) and the UK’s National Cyber Security Centre (NCSC), SbD has become a cornerstone of the UK government’s strategy. In this post, we will explore the successes, challenges, and risks overcome in implementing this approach across UK government systems.
Understanding Secure by Design
SbD focuses on integrating security features and practices into every stage of a product’s lifecycle—from initial concept and design to deployment and ongoing maintenance. This contrasts with traditional methods, where security was often retrofitted or considered only after a system’s development. By embedding security from the outset, organisations can significantly reduce vulnerabilities, minimise risks, and improve resilience against sophisticated attacks.
For UK government systems, this approach is not optional—it is essential. With sensitive citizen data and critical national infrastructure at stake, SbD supports robust cybersecurity aligned with the Government Cyber Security Strategy 2022-2030. This strategy aims to ensure that all government organisations have strong cybersecurity measures and can respond effectively to threats.
The Role of NIST and NCSC in Secure by Design
Both NIST and NCSC provide critical frameworks and guidance to enable SbD.
1. NIST’s Role
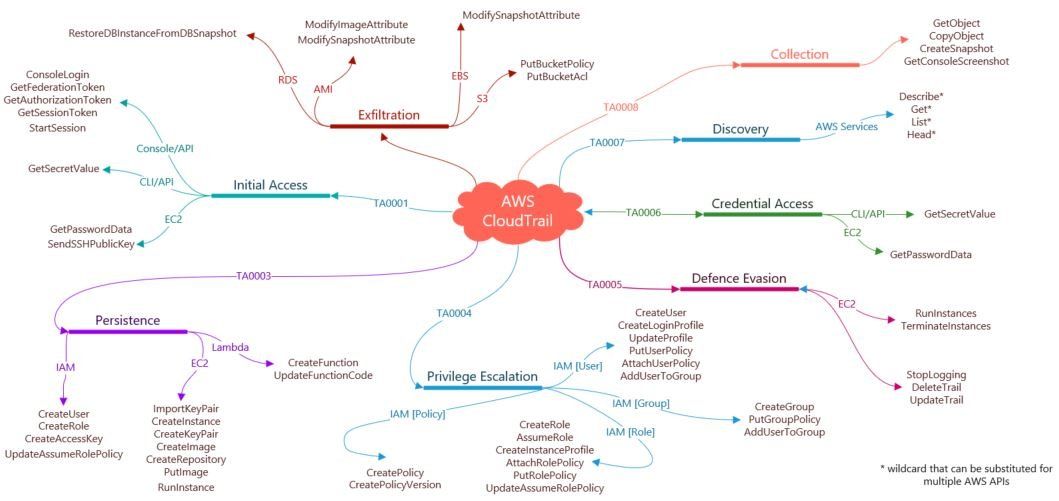
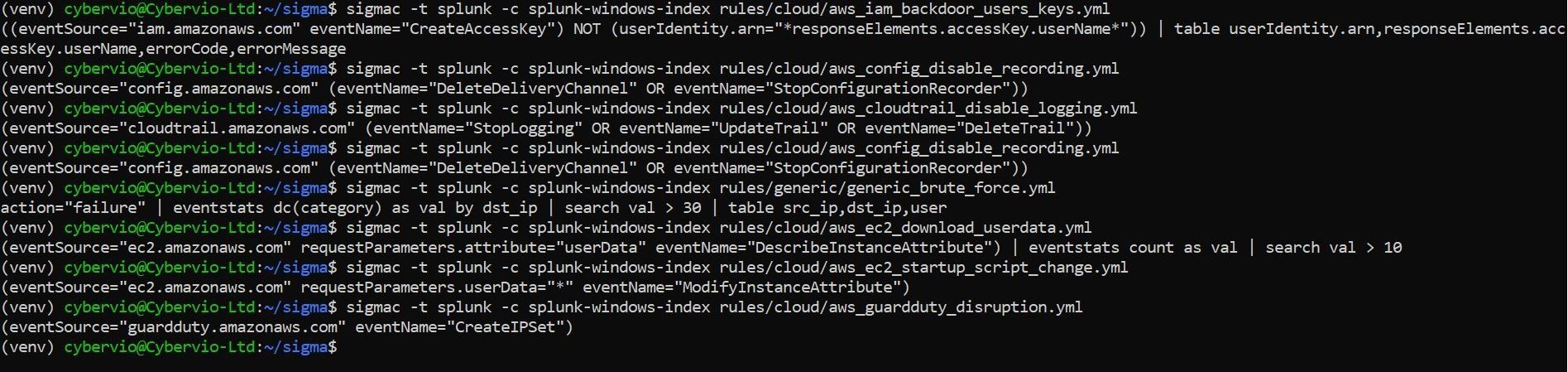
NIST’s Cybersecurity Framework (CSF) is a globally recognised standard. It provides a structured approach to managing cybersecurity risks, emphasising six core functions: Identify, Protect, Detect, Respond, Recover and Govern. For SbD, the NIST CSF offers actionable guidelines for integrating security at every stage of the system lifecycle. NIST’s SP 800-160 publication also focuses on systems security engineering, detailing principles for building secure and resilient systems.
2. NCSC’s Contributions
As the UK’s authority on cybersecurity, the NCSC provides tailored guidance to help government departments implement SbD. Its principles emphasise the importance of understanding risks, adopting secure development practices, and ensuring systems are resilient by design. Notable frameworks include the NCSC’s Cloud Security Principles and Cyber Assessment Framework (CAF), which align with SbD practices.
Together, these resources enable organisations to adopt a structured, internationally benchmarked approach to security while addressing UK-specific challenges.
Successes in Implementing Secure by Design
The UK government has made significant strides in implementing SbD, with notable successes including:
1. Improved Baseline Security Standards
The adoption of the NCSC’s CAF has helped standardise security requirements across government departments, ensuring a minimum baseline for protecting systems. This has been particularly effective in securing critical infrastructure and cloud services.
2. Increased Awareness and Training
SbD has driven greater awareness of cybersecurity among developers and system architects. Training programs emphasising secure coding practices and system engineering principles have reduced common vulnerabilities such as injection flaws and misconfigurations.
3. Resilience Against Attacks
By embedding threat modelling and security testing in the development cycle, government systems have become more resilient against cyberattacks. For instance, systems designed with robust identity and access management (IAM) features have successfully mitigated risks associated with unauthorised access.
4. Alignment with International Standards
The integration of NIST frameworks ensures that UK government systems align with international cybersecurity best practices. This fosters better collaboration with global partners and enhances trust in cross-border data exchanges.
Challenges in Adopting Secure by Design
While the benefits are clear, implementing SbD is not without its challenges. Key obstacles include:
1. Legacy Systems
Many government departments rely on aging IT infrastructure, which was not designed with modern security principles in mind. Retrofitting these systems to align with SbD can be complex and costly, requiring significant resources.
2. Cultural Resistance
Shifting the mindset from a reactive to a proactive approach to security has been challenging. SbD requires buy-in from all stakeholders, including developers, managers, and policymakers. Resistance to change can slow adoption.
3. Skills Shortages
The demand for cybersecurity professionals with expertise in secure system design far exceeds supply. This shortage has been a barrier to fully implementing SbD across all government projects.
4. Balancing Security and Usability
Designing systems that are both secure and user-friendly remains a challenge. Overly stringent security measures can hinder usability, potentially leading to workarounds that undermine the system’s security.
Overcoming Risks and Challenges
To address these challenges, the UK government has adopted a range of strategies:
1. Legacy System Modernisation
A phased approach to modernising legacy systems has proven effective. By prioritising the most critical systems and leveraging secure migration practices, departments have reduced risks while minimising disruptions.
2. Cultural Transformation
Continuous engagement and education campaigns have fostered a culture of security awareness. For example, the introduction of mandatory cybersecurity training for civil servants has increased understanding and support for SbD principles.
3. Building a Skilled Workforce
Investments in cybersecurity education and apprenticeship programs are helping to bridge the skills gap. Collaborations with academic institutions and private sector partners have also bolstered talent pipelines.
4. Integrating User-Centered Design
To balance security and usability, the Government has adopted user-centered design principles. By involving end-users early in the design process, systems can be both secure and practical.
Key Lessons Learned
The UK government’s journey in implementing SbD offers several lessons:
• Early Investment Pays Dividends: The cost of addressing security issues during development is significantly lower than post-deployment remediation.
• Collaboration is Critical: Effective implementation requires close collaboration between cybersecurity experts, developers, and end-users.
• Adaptability is Key: Cyber threats evolve rapidly, so SbD must be an ongoing, iterative process rather than a one-time effort.
Future Directions
As technology continues to evolve, so too must SbD. Emerging trends such as artificial intelligence (AI) and quantum computing will introduce new challenges and opportunities. The UK government is already exploring how these technologies can be harnessed securely, with frameworks like NIST’s Post-Quantum Cryptography Standardisation providing valuable guidance.
Additionally, the push towards a “zero trust” architecture—where no entity is inherently trusted and verification is required for all access—will further strengthen the SbD approach.
Conclusion
Implementing SbD across UK government systems is a complex but essential undertaking. By leveraging guidance from NIST and NCSC, the Government has made significant progress in creating resilient systems capable of withstanding modern cyber threats. While challenges such as legacy systems, cultural resistance, and skills shortages persist, the successes achieved thus far demonstrate the value of embedding security at the core of system development.
As the cyber threat landscape continues to evolve, the UK Government’s commitment to SbD will remain a critical pillar of its cybersecurity strategy. Through collaboration, innovation, and adherence to international best practices, the UK can ensure that its systems remain secure, trustworthy, and fit for purpose in the digital age.